Blue Team Labs Online - Vortex

Brianna noticed her workstation lagging and received a LinkedIn login attempt notification from an unfamiliar device. Worried, she reported to the IT help desk. Jake now investigates to find and collect IOCs.
Security Operations
Tags: Wireshark TCPdump CyberChef BTL1 T1566 T1204
Scenario Jake, a Transgear Corp Incident Response analyst, delves into an alert from Brianna, who flagged unusual activity on her workstation. A week prior, enticed by an email promising Amazon gift cards, Brianna clicked a link, unknowingly downloading malware. This granted attackers access, enabling espionage: capturing credentials, file copying, and eavesdropping on video calls. Days later, Brianna noticed her workstation lagging and received a LinkedIn login attempt notification from an unfamiliar device. Worried, she reported to the IT help desk. Jake now investigates to find and collect IOCs.
Reference Blog: https://www.securityblue.team/blog/posts/understanding-smtp-traffic-in-plaintext-using-wireshark
Environment Awareness
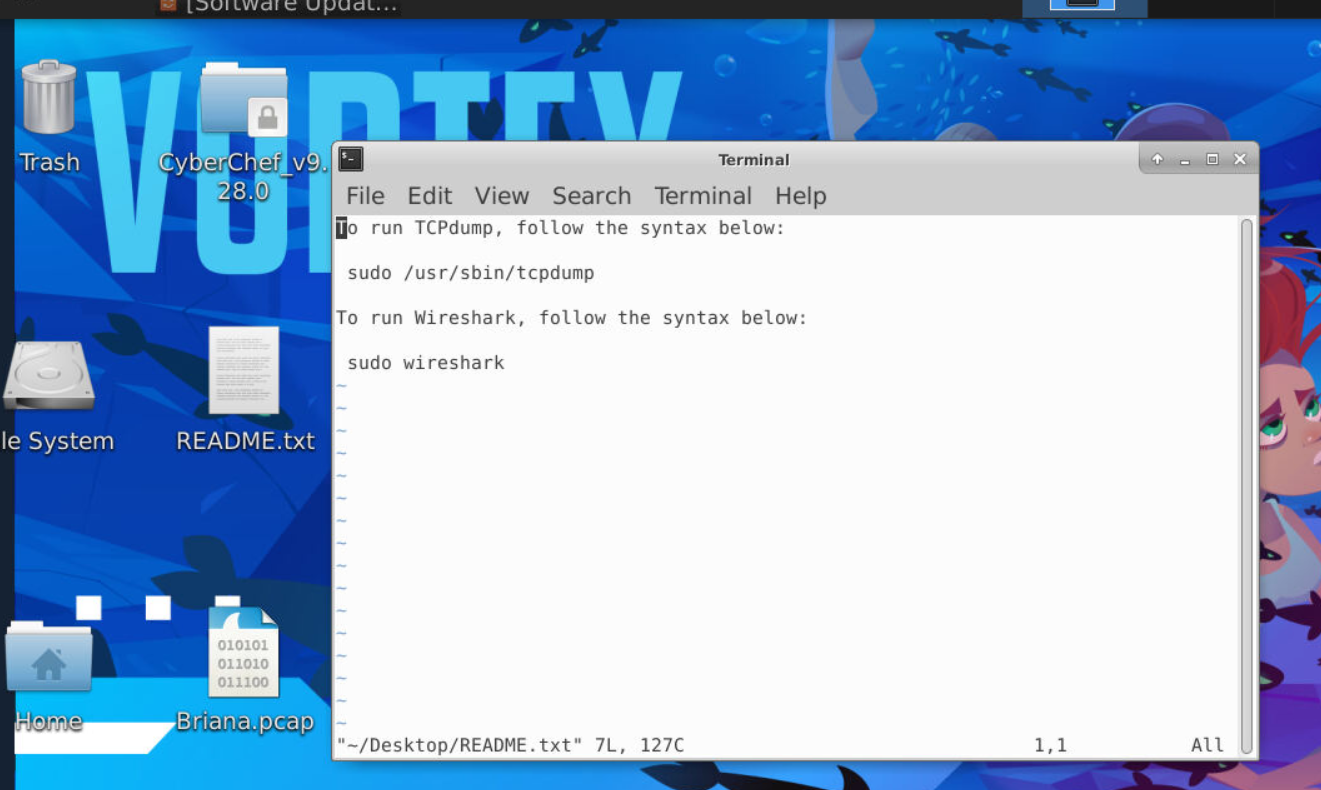 Lets see what we have, there is a note just in case we want to use Wireshark and tcpdump with root privilege and there is 1 pcap file on the desktop so we will have to dig into that file on Wireshark to complete this investigation.
Lets see what we have, there is a note just in case we want to use Wireshark and tcpdump with root privilege and there is 1 pcap file on the desktop so we will have to dig into that file on Wireshark to complete this investigation.
Investigation
Q1) What time did the suspected user system/browser connect to the malicious website? (Format: XX:XX:XX:XXXXXX)
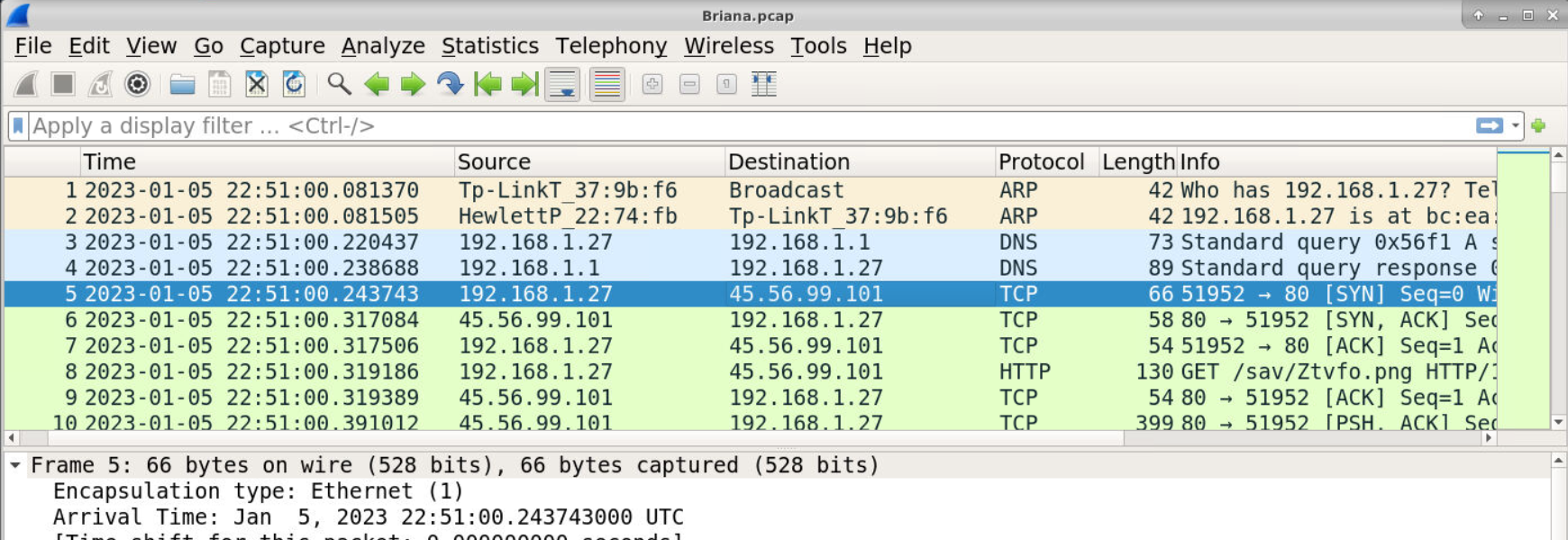 Afrer opened this pcap, First thing I noticed is HTTP request to download an image file from so-called malicious website so this image file has to be a trojan and 197.168.1.27 is Brianne's IP address.
Afrer opened this pcap, First thing I noticed is HTTP request to download an image file from so-called malicious website so this image file has to be a trojan and 197.168.1.27 is Brianne's IP address.
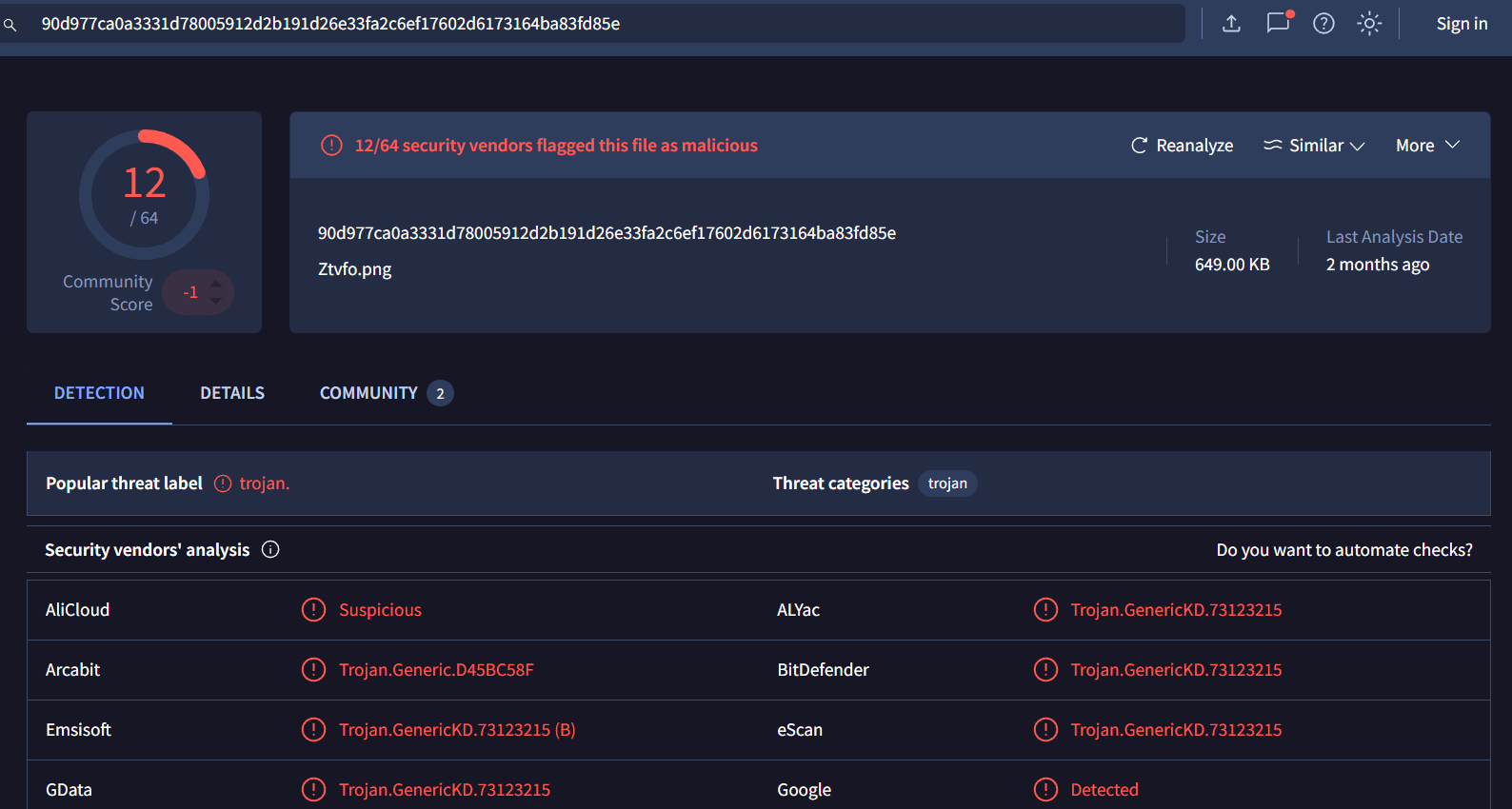
I exported this file out, calculate MD5 sum then search it on VirusTotal which return malicious as verdict.
So which time we should submit? normally I would put timestamp when ACK packet after SYN,ACK was sent back to source IP who request to establish a connection.
but in this case, Q1 accepted timestamp of the SYN packet.
Answer
22:51:00:243743Q2) What is Briana’s IP address? (Format: IP Address)
Answer
192.168.1.27Q3) What is Briana’s MAC/Ethernet address? What is the vendor name for the MAC address? (Format: MAC, Vendor Name)
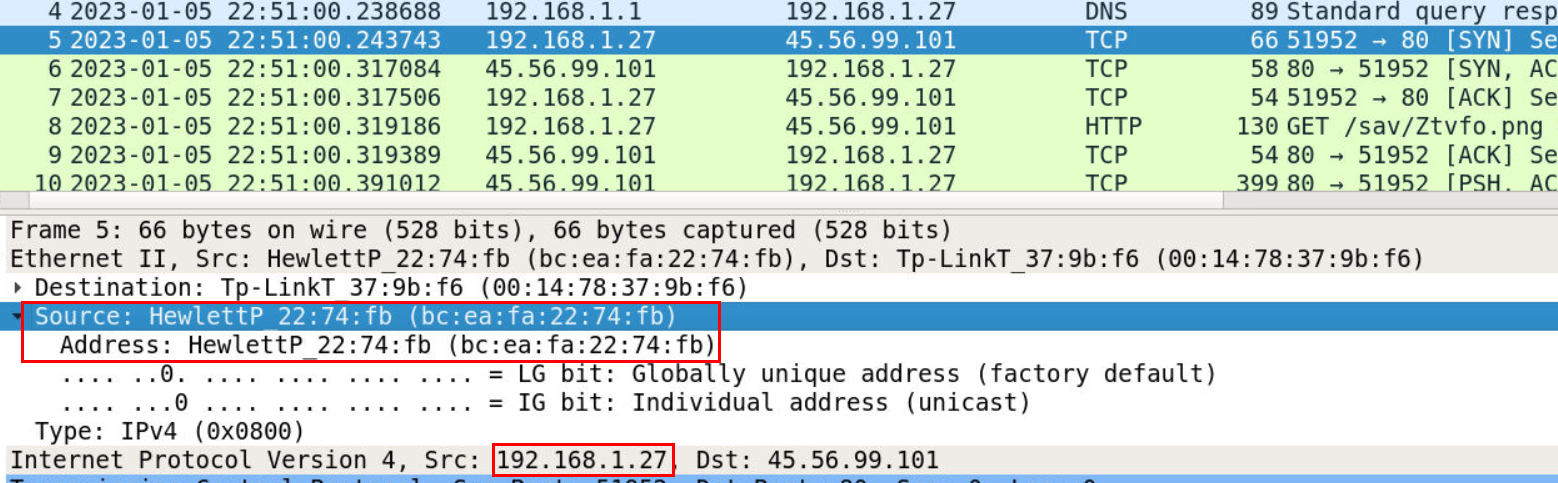 Take a look at packet inspection section then we will have MAC address and Vendor Name of this machine
Take a look at packet inspection section then we will have MAC address and Vendor Name of this machine
Answer
bc:ea:fa:22:74:fb, Hewlett-PackardQ4) What is Briana’s Windows machine name? (Format: Machine Name)
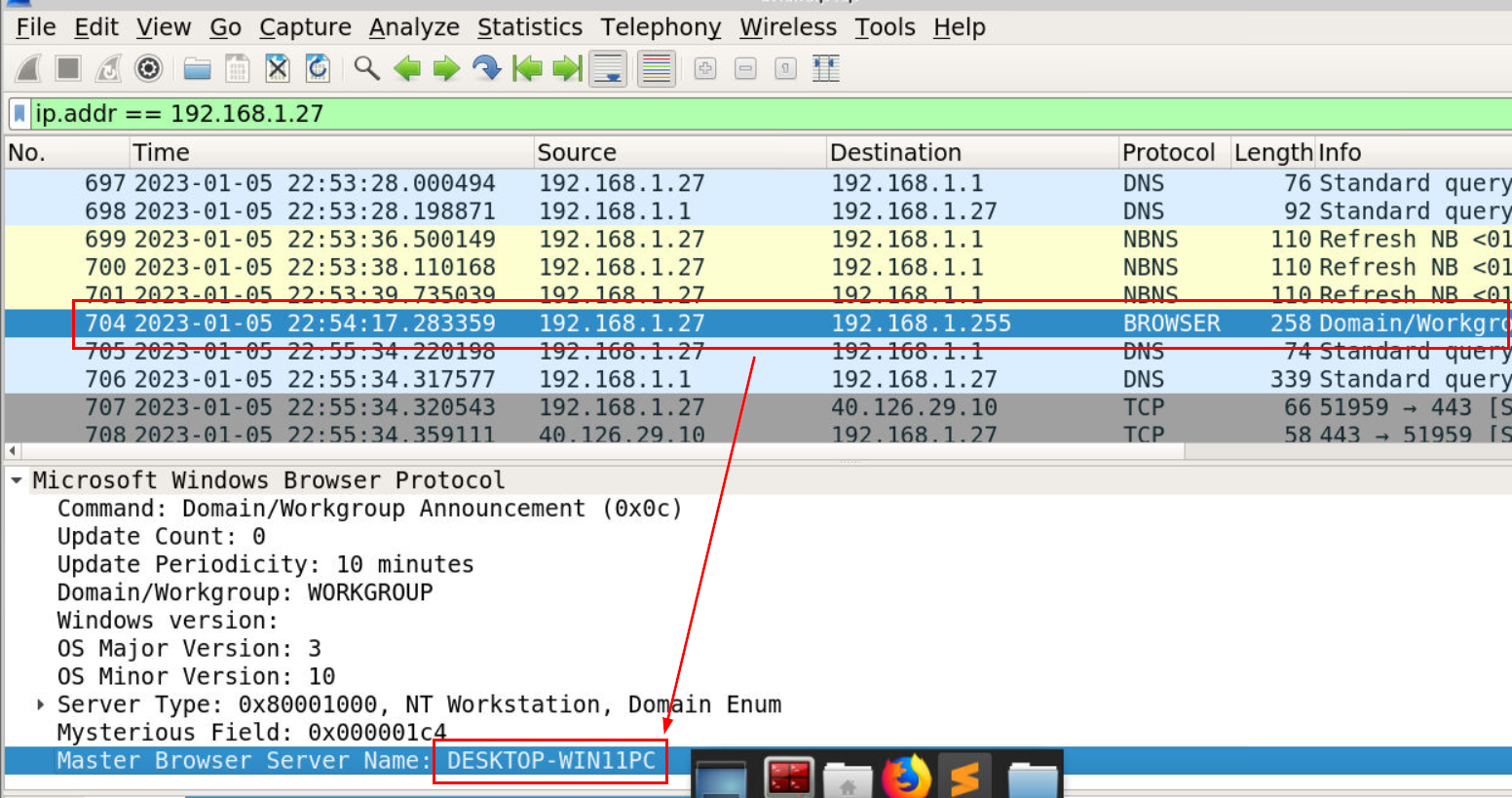 While taking a look at statistic, I found machine name of Brianna here in BROWSER protocol packet
While taking a look at statistic, I found machine name of Brianna here in BROWSER protocol packet
 but intended way might probably inspect SMTP communication which is the data exfiltration method that the malware used to send collected data to an attacker.
but intended way might probably inspect SMTP communication which is the data exfiltration method that the malware used to send collected data to an attacker.
Answer
DESKTOP-WIN11PCQ5) What is Briana’s Windows username? (Format: Username)
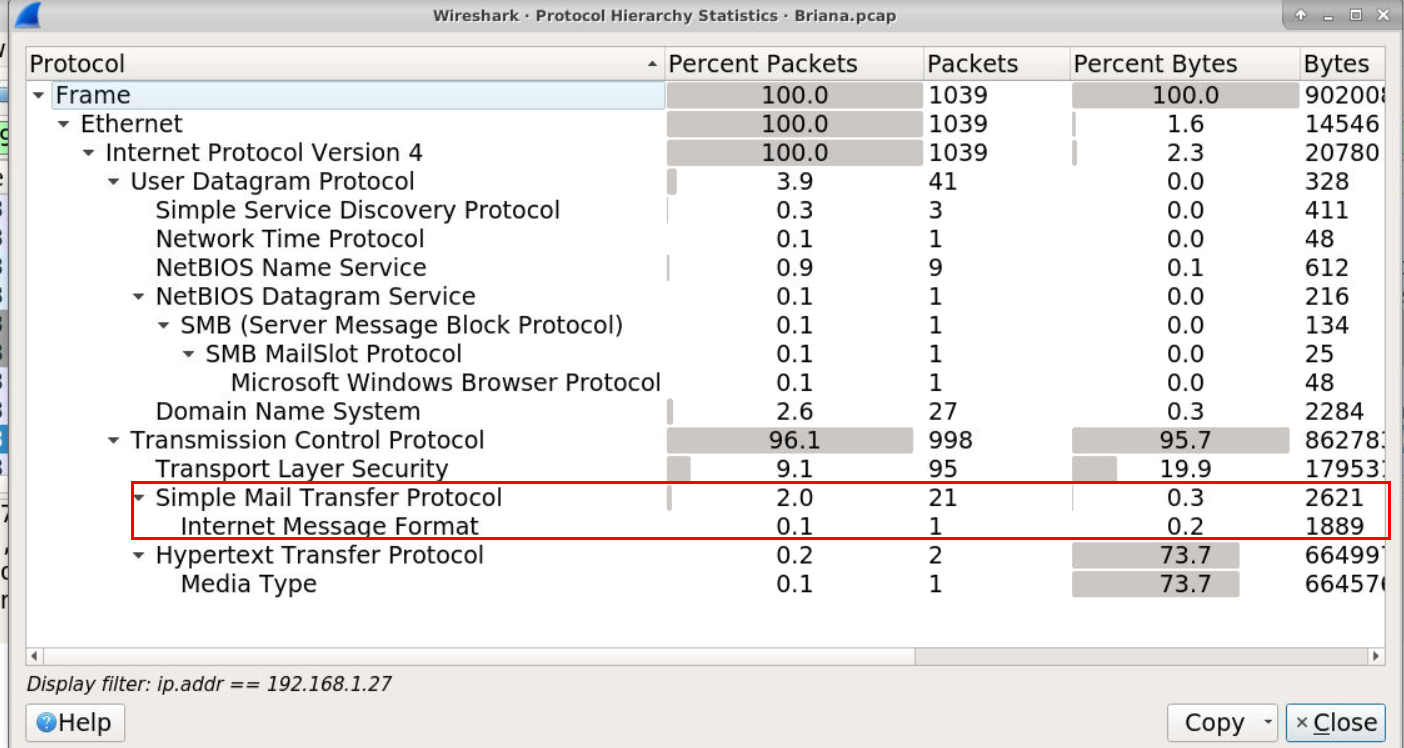
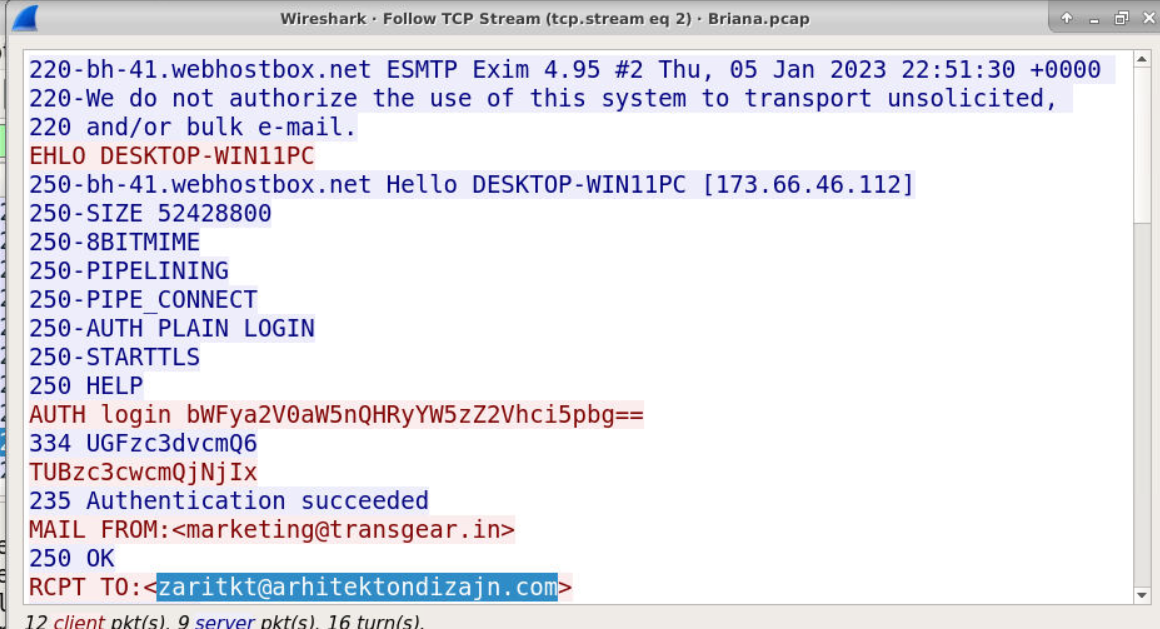 After taking a look at SMTP conversation we can see that its authenticated as marketing@transger.in and sent a mail to zaritkt@arhitektondizajn.com (Q6) and the content of this mail is username and password (Q9) stored on Brianna machine
After taking a look at SMTP conversation we can see that its authenticated as marketing@transger.in and sent a mail to zaritkt@arhitektondizajn.com (Q6) and the content of this mail is username and password (Q9) stored on Brianna machine
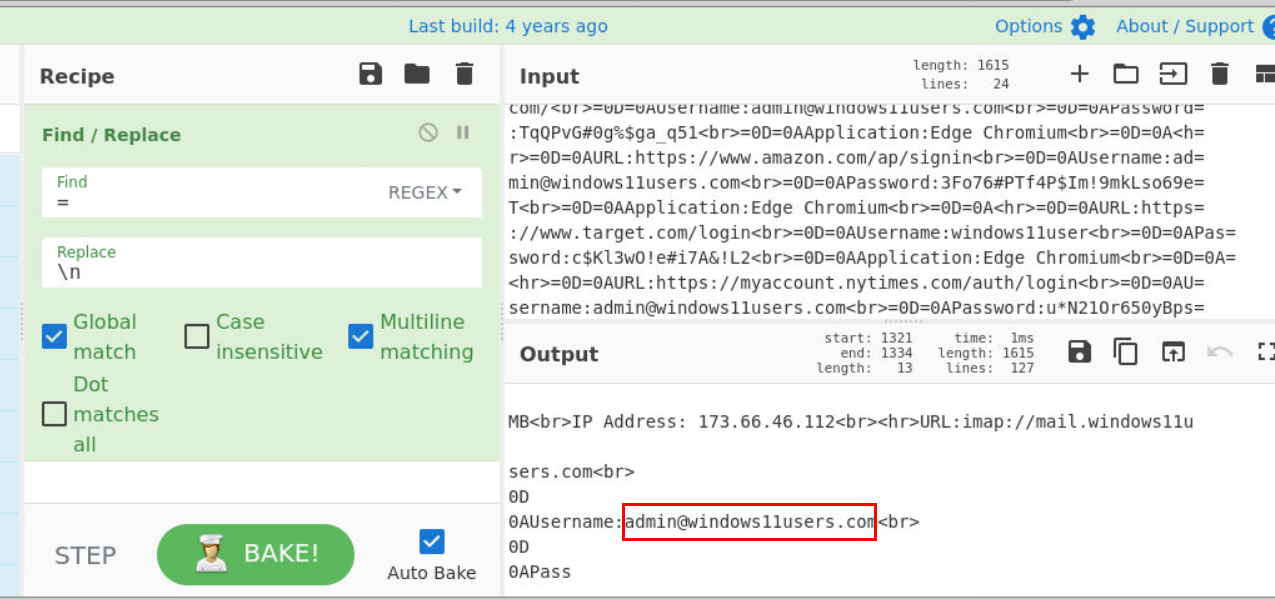
I putted it to CyberChef and make it look a little less confusing but we will eventually find username of Brianna here
Answer
admin@windows11users.comQ6) What email address was the attacker sending data to? (Format: name@domain.tld)
Answer
zaritkt@arhitektondizajn.comQ7) What type of CPU does Briana’s computer use? (Format: CPU Name)
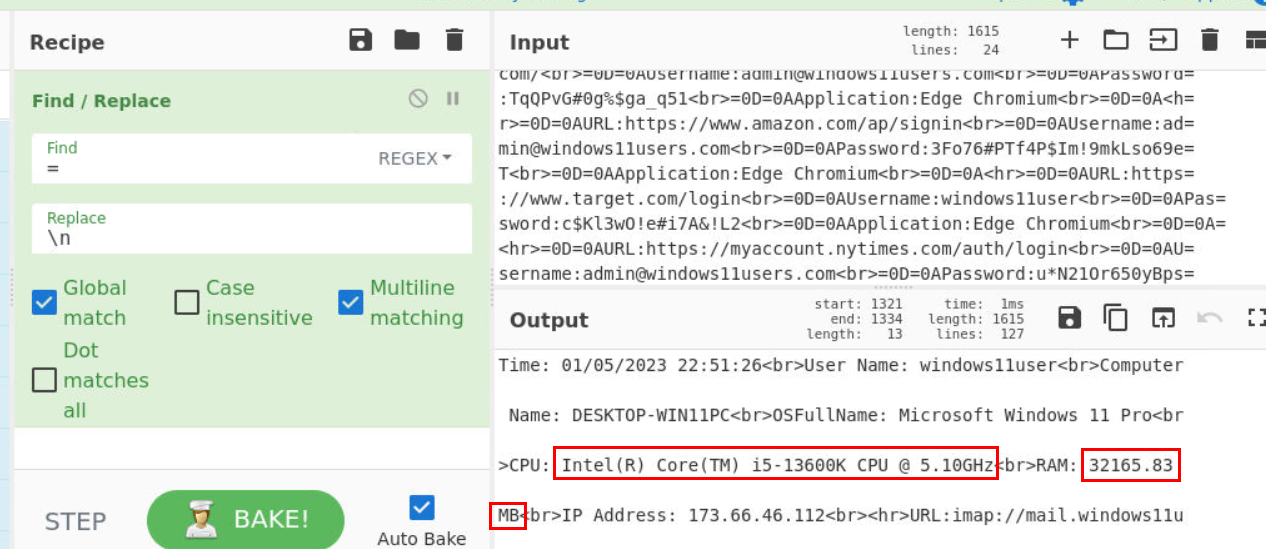 System information is the first on this mail which also included CPU and RAM (Q8) info right here
System information is the first on this mail which also included CPU and RAM (Q8) info right here
Answer
Intel(R) Core(TM) i5-13600K CPU @ 5.10GHzQ8) How much RAM does Briana’s computer have—in GBs? (Format: XXGB)
Answer
32GBQ9) What type of account login data was stolen by the attacker? (Format: Data1, Data2)
Answer
Passwords, UsernamesQ10) What are the username and password related to the Amazon account? (Format: Username, Password)
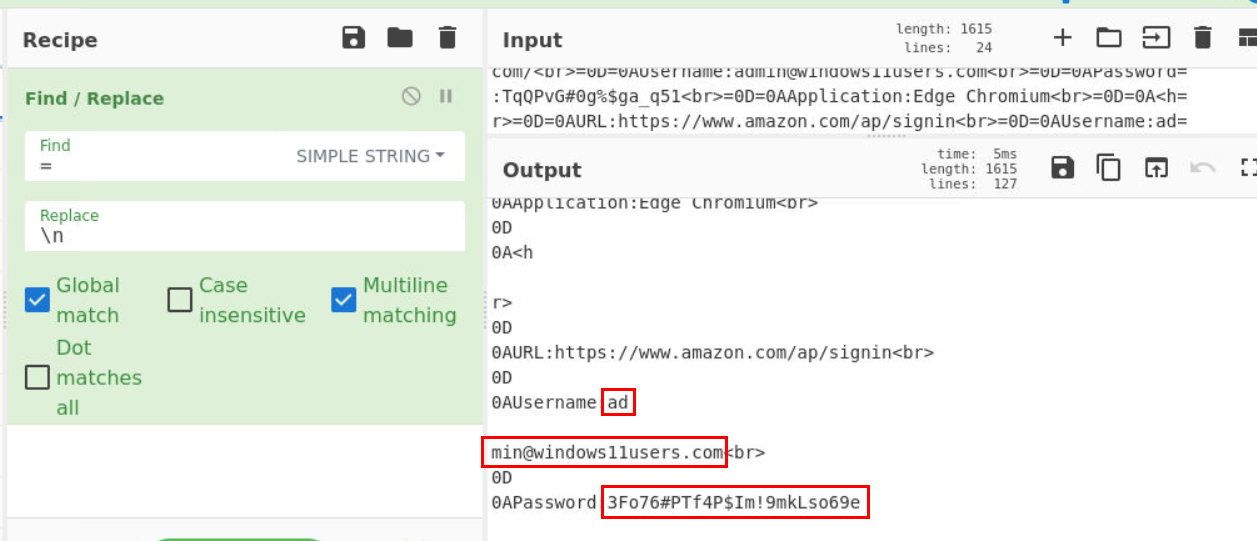 Lets search for "amazon" then we should have both username and password right here.
Lets search for "amazon" then we should have both username and password right here.
Answer
admin@windows11users.com, 3Fo76#PTf4P$Im!9mkLso69eQ11) What username did Briana use to authenticate to webhostbox[.]net? Can you decode it? (Format: Username)
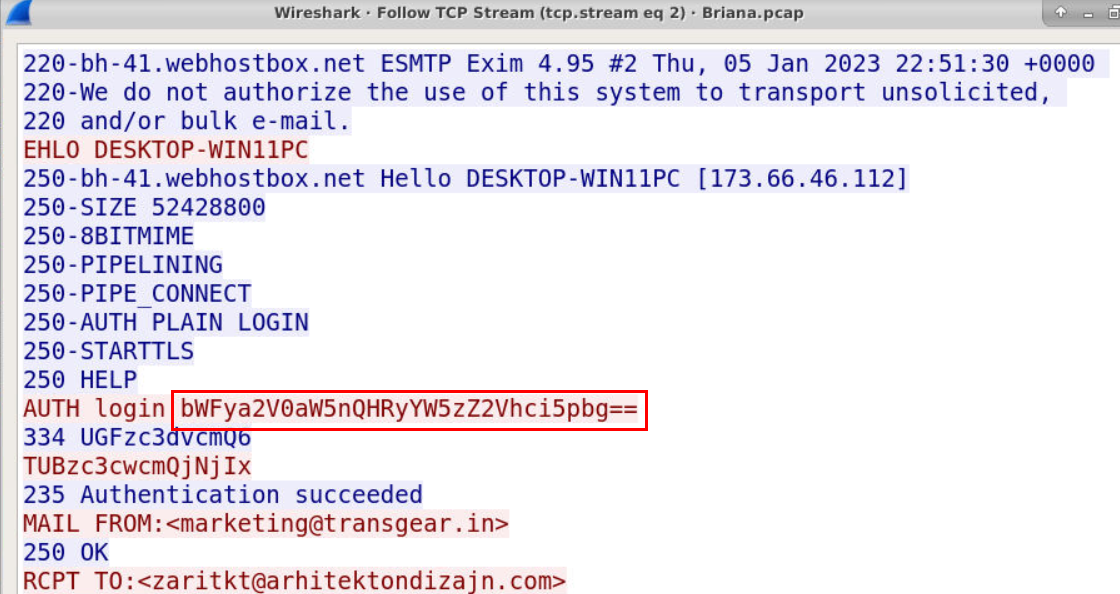
We already know username but lets confirm it by decoding these base64 strings along with password for Q12
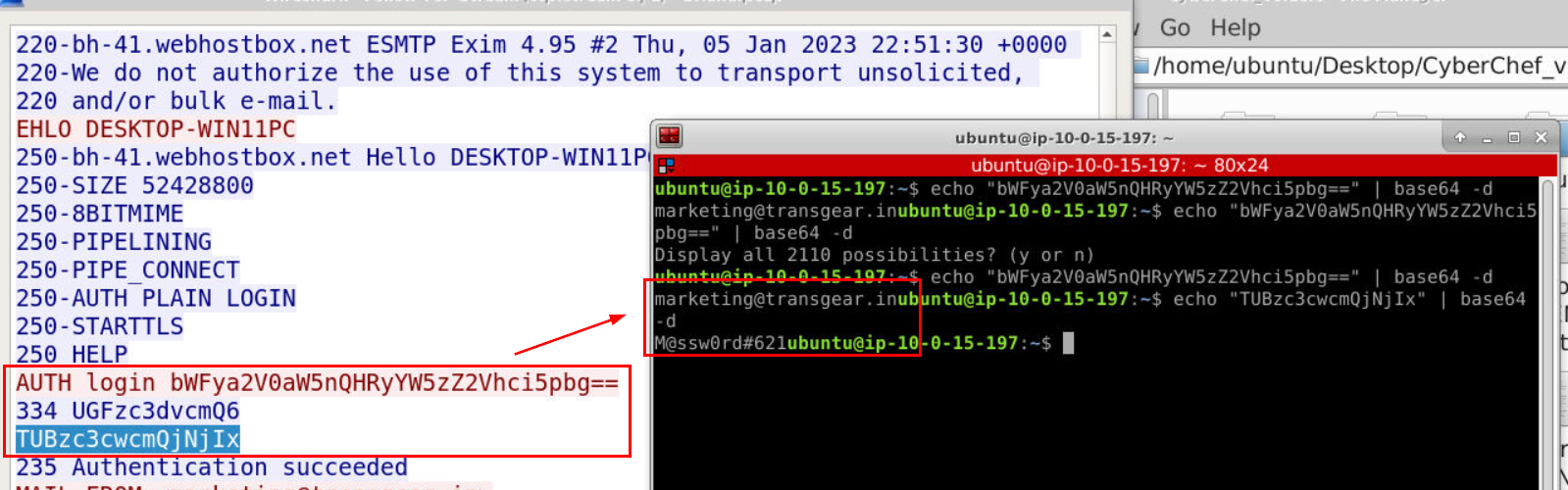 Alright we got the right one, along with password that used to authenticate.
Alright we got the right one, along with password that used to authenticate.
Answer
marketing@transgear.inQ12) What password did Briana use to authenticate to webhostbox[.]net? Can you decode it? (Format: Password)
Answer
M@ssw0rd#621 https://blueteamlabs.online/achievement/share/52929/227
https://blueteamlabs.online/achievement/share/52929/227
Summary
Brianna downloaded a malware then executed it resulting data collection on her machine then sending back to the attacker email address that including Brianna's system information and user credentials saved on her machine.
Timeline
- 2023-01-05 22:51:00 : A request was sent to download
- 2023-01-05 22:51:30 : Data exfiltration via SMTP occurred
- 2023-01-05 22:53:09 : SMTP connection terminated
IOCs
45[.]56[.]99[.]101zaritkt@arhitektondizajn[.]com